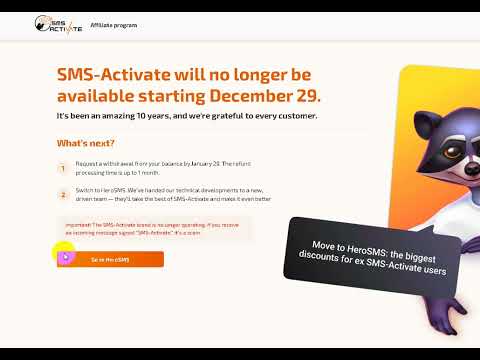
The reliance on SMS verification for online account security has become a standard practice across almost every digital platform. From social media accounts to banking services and professional communication tools, companies frequently require a phone number to confirm identity or prevent fraudulent sign-ups. For users who prioritize privacy, need to scale their operations, or simply operate in regions where local number acquisition is cumbersome, SMS-activate provided a reliable hub for virtual numbers. However, shifts in the market and changes in service availability have pushed many users to look for reliable sms activate alternatives to maintain their digital workflows without interruption.
Understanding the Role of SMS Verification in Digital Identity
SMS verification serves as a critical checkpoint in the digital world. By linking a real-world phone number to a digital profile, businesses can reduce the prevalence of bot networks, spam accounts, and malicious actors trying to gain unauthorized access to data. This process, often referred to as two-factor authentication, is the backbone of trust for many applications, confirming that the individual on the other side of the screen is a unique participant. For developers and power users, managing thousands of these verifications at scale is a significant logistical challenge that requires specialized infrastructure.
When you engage with a platform that offers virtual numbers, you are essentially renting access to a global telephony infrastructure that can receive incoming SMS messages for a defined duration. This is essential for users who either do not want to expose their personal phone number to multiple third-party services or for developers who need to test their applications across different international markets. The architecture of these services must be robust enough to handle high volumes of incoming messages while maintaining the privacy of the end user. As the digital landscape evolves, so too do the requirements for security and efficiency within these services.
Why Users Seek Alternatives to Established Providers
The marketplace for virtual SMS reception is dynamic and prone to rapid changes. Users often look for new providers when the service they were previously using, such as SMS-activate, experiences downtime, changes its geographic coverage, or modifies its pricing structures. When a core tool in your workflow fails to deliver messages, the consequences can range from minor account login issues to the disruption of large-scale automation projects. Having a secondary or tertiary provider in your toolkit is a strategic necessity for anyone involved in digital marketing, software development, or affiliate management.
Another driving factor in the search for alternatives is the need for enhanced functionality. As projects grow in complexity, users often require more than just simple message reception. This might include robust API availability, specific country coverage that was previously unavailable, or better user dashboards that allow for the management of multiple sessions simultaneously. Security concerns also play a significant role. Users frequently look for platforms that demonstrate higher transparency, offer clearer privacy policies regarding data retention, and provide a more stable, long-term commitment to their service base. Choosing the wrong provider can lead to leaked data or, at the very least, a frustrating loss of time.
Evaluating Service Reliability and Security Standards
Reliability is measured by the speed and consistency of message delivery. In an ideal scenario, a SMS verification code should arrive within seconds of being requested by the third-party service. Delays in this process can cause authentication tokens to expire, leading to the need for multiple requests, which might ultimately result in a temporary or permanent block on your account from the receiving platform. A high-quality alternative is one that maintains direct connections with mobile network providers, minimizing the chance of bottlenecking or lost messages during peak demand times.
Security goes beyond the simple delivery of text. It encompasses the entire pipeline, from the moment a number is requested to the deletion of personal data after the task is completed. You should examine whether a provider uses encrypted transmission protocols for their API and how they handle the anonymity of their users. Look for companies that provide clear documentation on their data practices and that do not require invasive personal information just to access a testing or temporary number service. A professional provider will always prioritize the security of the communication channel, ensuring that verification codes are not intercepted or accessed by unauthorized third parties.
Key Factors When Choosing Your Next Provider
Selecting the right service requires a careful balance of cost, accessibility, and technical capability. Not all virtual number platforms are created equal, and your choice should be dictated by your specific use case. Whether you are performing one-off verifications or running an automated system for thousands of users, the following checklist should guide your decision-making process.
- Geographic coverage: Does the platform offer numbers from the specific regions or countries required for your particular applications?
- API documentation: Is the platform developer-friendly, providing clean code snippets and reliable endpoints for automated workflows?
- Scalability: Can the service handle a sudden surge in requests without degrading performance or losing messages?
- Cost structure: Look for transparent pricing. Avoid platforms with hidden fees or complex, confusing subscription models that make it hard to track your spending.
- Dashboard usability: A clean, intuitive interface allows you to monitor message history and balance status effectively.
By keeping these factors in mind, you can narrow down the field of potential candidates significantly. Many platforms offer free trials or small initial balance options, which are perfect for testing the efficacy of their network before committing to a larger project. Always perform a stress test on a small scale to verify the responsiveness of the chosen provider before moving your production-level traffic to their infrastructure.
Comparing Different Market Options for Virtual Numbers
Understanding how different options stack up against each other is vital for long-term project planning. The following table illustrates the typical categories of features that should influence your comparison of various SMS verification platforms.
| Feature Category | Low-End Solution | Professional-Grade Solution |
|---|---|---|
| API Integration | Basic or None | Robust, RESTful, and well-documented |
| Number Variety | Limited availability | Global coverage across multiple operators |
| Throughput Capability | Moderate, prone to delays | High-concurrency support |
| Support Quality | Community forums only | Dedicated ticket system and SLA |
| Security Protocols | Minimal encryption | End-to-end data protection |
While low-end solutions might appear attractive due to their headline pricing, the hidden cost of system downtime or failed verifications can far outweigh the savings. Professional-grade platforms invest heavily in their infrastructure and support networks, providing a more stable environment for high-frequency users. When moving away from a known entity like SMS-activate, ensure that you are not just shifting to a cheaper alternative, but to one that provides verified improvements in stability and data security.
Best Practices for Integration and Scalability
Implementing a new SMS service into your existing business workflow should be approached with caution and methodical planning. The transition from one provider to another is an opportunity to optimize your system. You should first ensure that your code is modular, allowing you to swap out your SMS gateway provider without having to rewrite your entire backend logic. This involves using a configuration file to store your API keys and endpoints, which can be updated instantly if the need arises to switch services again in the future.
To ensure scalability, consider implementing a queue system for your SMS requests. If your traffic spikes, having a message queue will prevent your application from overloading the provider’s infrastructure. This buffer system allows your requests to be processed sequentially and provides a fallback mechanism in case a specific node or number provider is experiencing latency. Monitoring is also key; logs should capture not just the primary outcome of the SMS request, but also response times and any error codes returned by the gateway. This data is invaluable for debugging and for holding service providers accountable for their advertised speeds and reliability.
- Define your requirements clearly before shopping for a new provider.
- Audit your current code for hard-coded API endpoints and migrate those to a dynamic configuration file.
- Set up an automated alert system in your dashboard to notify you of latency issues or balance depletion.
- Run a pilot test with a small set of accounts to ensure the quality of the incoming messages.
- Monitor delivery rates over a 48-hour period to establish a baseline of reliability.
- If the performance meets your metrics, proceed with a gradual rollout of your production traffic.
Navigating Privacy and Customer Support Requirements
Privacy is the primary concern for users operating in the digital sphere. When you use public or virtual numbers, you are essentially leasing a temporary identity. It is imperative to perform due diligence on the privacy policy of the platform. Always look for providers that explicitly state how they handle message content and whether they keep records of the verification codes received. A trustworthy firm will treat all incoming SMS messages as ephemeral and will not store them longer than necessary for you to retrieve your code. If a provider offers an option to auto-delete messages immediately after retrieval, this is a strong sign of a privacy-focused company.
Customer support is the final pillar of a successful business relationship with a service provider. Because SMS verification can be time-sensitive, having access to human-led, responsive support is paramount. Before signing up, test their communication channels. Send a simple inquiry about their API limits or coverage availability to see how quickly they respond. A lack of responsiveness during your trial period is a stark indicator of the service level you can expect during an emergency. Prioritize platforms that offer multi-channel support, including ticketing systems that provide a historical record of your technical queries and their resolutions, as this creates a trackable path for troubleshooting complex issues.
Beyond individual support, seek out providers that maintain a status page or an active community channel. Real-time updates regarding network maintenance or regional service outages allow you to take proactive steps, such as pausing your automated workflows, before they become a larger problem. By actively managing these relationships and maintaining a clear view of your infrastructure requirements, you can build a sustainable and secure setup that enables your digital activities to thrive, regardless of the fluctuations in the external market for virtual number solutions.
Understanding these elements helps in building a mature approach to digital identity management. Whether you are a solo entrepreneur experimenting with new projects or a team lead managing large-scale automated infrastructures, the choice of your SMS service impacts your bottom line and your operational efficiency. By prioritizing security, scalability, and robust support, you ensure that your projects remain resilient. The evolving nature of the internet requires you to stay agile, prepared to adapt your tools, and consistently focused on the performance metrics that define the success of your digital operations.
The landscape of virtual telephony will continue to shift as platforms improve their own detection of non-human traffic. This creates a cat-and-mouse game between providers and the services you are trying to verify. Staying aware of these market realities ensures that you are not just selecting a tool for today, but developing a framework that can handle the challenges of tomorrow. Always keep your focus on the technical requirements of your project and ensure that your chosen solutions provide the necessary transparency and performance to support your goals.
As you move forward, remember to periodically audit your providers. Even if a service starts off strong, internal company changes, shifts in server infrastructure, or changes in carrier partnerships can affect the quality of service. A proactive approach to auditing your vendors will prevent the sudden realization that your systems are down during critical business hours. Document your workflows, maintain a list of secondary providers, and keep your API integration clean and modular. This defensive posture is the hallmark of professional operations and ensures long-term success in the competitive digital environment.
Finally, consider the human element of your operations. While automation is the goal, the management of these services is inherently a human task. Investing time in understanding the underlying technology—how SMS routing works, the implications of VoIP versus mobile-originated numbers, and the regulatory environment in your target countries—will give you a significant advantage. This foundational knowledge allows you to troubleshoot faster, communicate more effectively with support, and identify higher-quality vendors that are offering genuine value rather than just a quick fix. By staying informed and strategic, you build a foundation that supports your vision for years to come.
